How to get people to pay attention to phone, computer security notifications
Using brain data, eye-tracking data and field-study data, a group of BYU researchers have confirmed something about our interaction with security warnings on computers and phones: the more we see them, the more we tune them out.
But the major study, led by information systems professors Anthony Vance, Bonnie Anderson and Jeff Jenkins, also finds that slight changes to the appearance of warnings help users pay attention to and adhere to warnings 20 percent more of the time.
The National Science Foundation-sponsored study, which includes a longitudinal experiment that discovers how habituation develops over the course of a week, appears in the June 2018 issue of MIS Quarterly and provides the most complete view to date of the problem of habituation to security warnings.
"The problem—and something everyone has experienced—is that warnings just fade away and disappear over time in our consciousness because we're exposed to them so often," said Vance, lead author and associate professor of information systems.
Vance, Anderson and Jenkins, along with BYU neuroscience professor Brock Kirwan, have been studying habituation for years, however in each case they looked at a single snapshot of behavior or neural response. This study, however, combined a five-day lab experiment, where subjects' neural and visual responses to warnings were recorded with a three-week field study of users interacting naturally with privacy permission warnings.
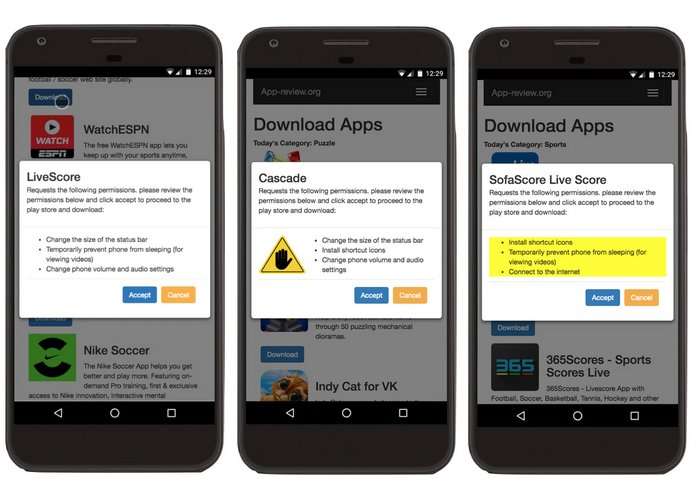
For the field study, the team required participants to install and evaluate three apps every day for 15 days from an Android app store they designed. Each time subjects selected an app to download, a warning popped up that listed permissions the app requested to access or modify data, some of which were risky (e.g. "Sell your web-browsing data," or "Record microphone audio any time"). Some participants got the same-looking warning every time while another group got polymorphic warnings, or warnings that changed in appearance each time.
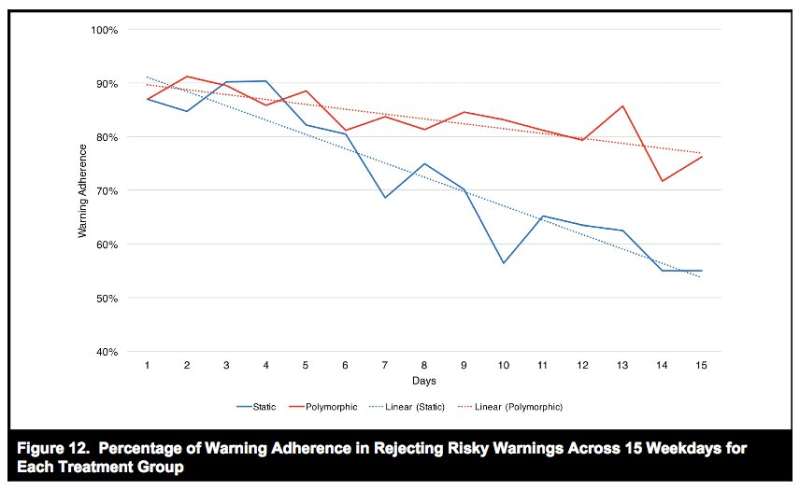
Android users who installed apps with risky permission were recorded as disregarding the warning. The researchers found participants who were exposed to the changing set of warnings still adhered to them 76 percent of the time at the end of the 15 days. Those who saw static warnings only adhered to them 55 percent of the time.
"Even using a few variations can have a substantial effect over time," said Anderson, professor and chair of the BYU Department of information Systems. "The trick is to get the variations to the point where people pay attention without being annoyed."
In the fMRI and eye-tracking lab study, researchers found that people quickly habituated to repeated warnings, both in terms of decreased neural activity and fewer eye fixations. However, they also found that a polymorphic warning was able to significantly sustain attention over time.
Researchers said that while users should remain vigilant about security warnings, the findings are not an indictment of their behavior. For them, the bigger application is for those creating the software.
"System designers need to understand this is how the brain works, and they need to be as judicious as possible with the number of warnings they present," Vance said. "Secondly, if they can add some visual novelty to the warning, that really helps the brain recapture attention."
More information: dx.doi.org/10.25300/MISQ/2018/14124





















